BAYC: Mutant Ape game
Posted on 26 Sep 2021 in security • Tagged with security, reverse, javascript, cryptocurrency, NFT • 2 min read
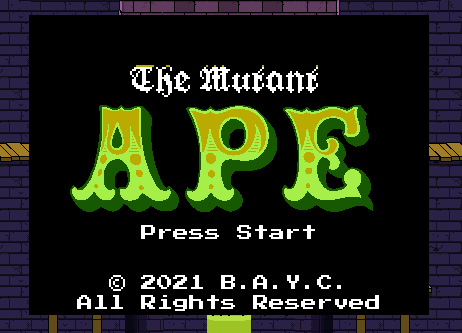
A different kind of article about a game organized by the Bored Ape Yach Club a few weeks ago. The deal was to complete five levels of a difficult game to get a Proof of attendance token.
As a few weeks have pass since the end of the game I will share a few tips to win every time as the game is written in JavaScript.
The game is located at https://2dengine.com/mutantarcade/
Note: it seems that you are directly in the last level (5/5) using the link above. You can find an archive with the JS files here.
Continue reading